Creating An Azure Credential the Easy Way in Windows Using Powershell and get_azure_cred.ps1
We have created some helpful scripts in our public Github repository. One of those is a script called get_azure_cred.ps1, which runs in Windows and Powershell and will:
- Log you into your Azure account
- Create an application for you in your Active Directory
- Create an associated service principal for you in your Active Directory (which can be used to login on your behalf)
- Create a limited permission role
- Map the service principal to the limited permission role
- Output the parameters you will need to enter into ParkMyCloud.
- You will need to have sufficient privileges within Azure to accomplish the above tasks.
- You may also need to set the proper permissions to run powershell scripts: Set-ExecutionPolicy RemoteSigned
- Create a directory to pull this repository to your Windows system (e.g., c:\users\<you>\git
- Change to that directory: cd ~/git
- Clone the repository: https://github.com/parkmycloud/useful_tools.git (I suggest using Git-Desktop)
- Set your branch to the latest version: (e.g., git branch v1.2)
- Change to the appropriate directory: cd ~\git\useful_tools\powershell
- Execute the script shown: .\get_azure_cred.ps1
- Follow the directions.
cd ~\gituseful_tools\powershell
./get_azure_cred.ps1
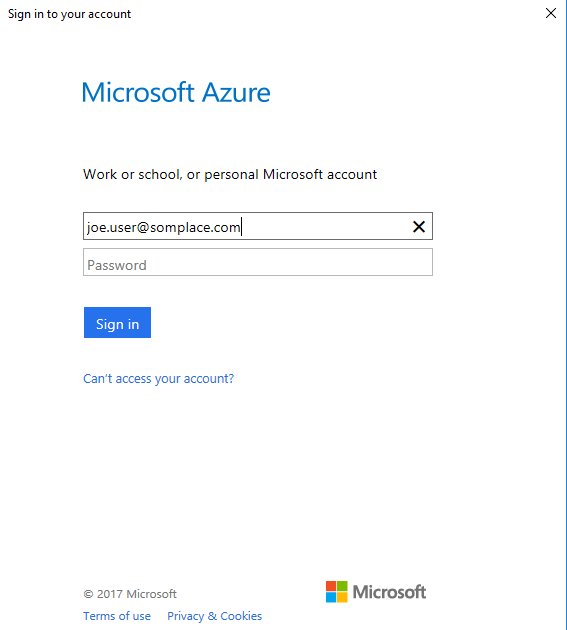
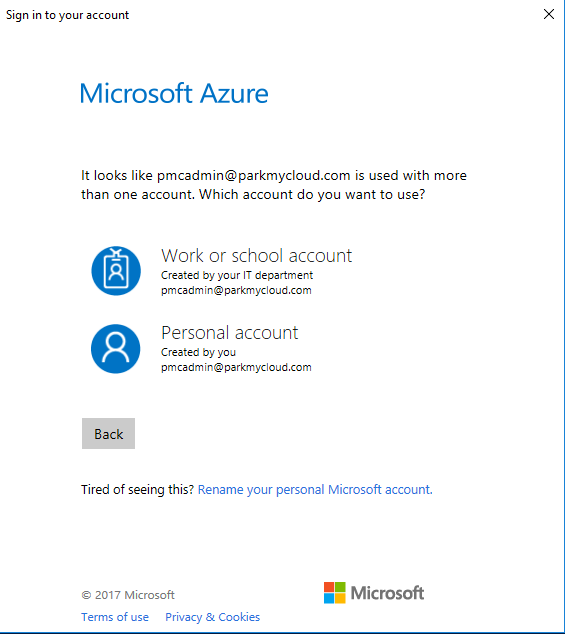
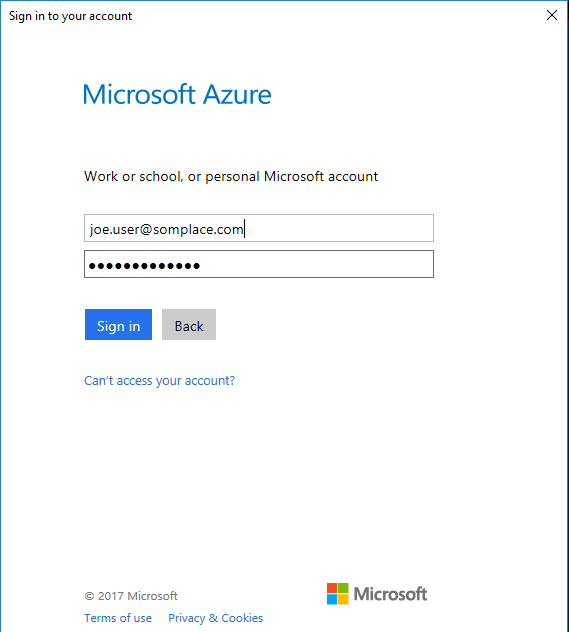
Logging into Azure:
Here are the subscriptions associated with your account:
My-Subscription-1
My-Subscription-2
Enter the subscription you want to use:
My-Subscription-1
Need to create a ParkMyCloud application in your subscription.
Here's the catch: It must be unique.
What do you want to call it? (e.g., ParkMyCloud Azure Dev): PMC Azure Dev
Enter password for your application: parkmycloud1
Re-enter your password: parkmycloud1
Created service principal for application.
Created limited access role for app.
Waiting on Service Principal to show up in AD
Service Principal 0a12340-57qg-0f56-0234-0a1234b5cd67 found.
Role has been mapped to service principal for application.
Subscription ID: 00aaa000-00aa-0a00-0000-0a0000a0aa00
Tenant ID: 0b00b0b0-0000-0000-00b0-bbb0b0b000bb
App ID: 000kkk0-00kk-0000-k00k-00kk0000000k
API Access Key: parkmycloud!
Enter these on the Azure credential page in ParkMyCloud.
There is a hidden directory created called ~\.PMCAzure which will store information about each step of the process:
cd ~\.PMCAzure
ls
Directory: C:\Users\<you>\.PMCAzure
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/5/2017 3:39 PM 374 PMCAzureAccountLog
-a---- 1/5/2017 3:40 PM 894 PMCAzureAppLog
-a---- 1/5/2017 3:39 PM 572 PMCAzureLoginLog
-a---- 1/5/2017 3:40 PM 1018 PMCAzureRoleLog
-a---- 1/5/2017 3:40 PM 1078 PMCAzureRoleMapLog
-a---- 1/5/2017 3:40 PM 770 PMCAzureServicePrincipalLog
-a---- 1/5/2017 3:40 PM 1962 PMCExampleAzureRole.json
Related Articles
Creating An Azure Cred the Easy Way In Linux Using azure-cli and get_azure_cred.sh Script
We have created some helpful scripts in our public Github repository. One of those is a script called get_azure_cred.sh, which runs in Ubuntu Linux and will: Install nodejs, npm and azure-cli (if they are not already installed) Log you into your ...Creating An Azure Credential For ParkMyCloud
Goal The goal of this process is to configure limited access for ParkMyCloud to an Azure subscription. To do this you will need to obtain the following pieces of information to create the ParkMyCloud Azure credential: Subscription ID Tenant ID App ID ...Creating An Azure Credential Manually Using Windows Powershell
1. Install Azure Cmdlets in Windows Powershell: Open a Powershell window as administrator Run the following commands: Install-Module AzureRM Install-Module Azure You can verify proper installation by typing the following command: Get-Module Output: ...Creating an Azure Credential Manually Using Azure CLI
1. Install azure CLI (linux shown below) using NodeJS install: if nodejs, npm and/or azure-cli are not installed: curl -sL https://deb.nodesource.com/setup_7.x | sudo -E bash - sudo apt-get install -y nodejs sudo npm install -g azure-cli 2. Login ...Setting Up Azure Active Directory (Free Version) As A SAML IdP Server for ParkMyCloud
When you followed our article on creating an Azure credential, that process included creating an application in Azure. We are now going to revisit one of those applications and configure some of its settings to configure Azure Active Directory as an ...